As a React developer with over 10 years of experience, I’ve seen the framework evolve and grow immensely in popularity. React’s component-based architecture makes building interactive UIs simple, but it also introduces unique security challenges that many developers overlook.
In this article, I’ll share practical insights into common security vulnerabilities in React components. I’ll walk you through how to identify and fix these issues, ensuring your React applications stay safe, especially when dealing with sensitive user data or enterprise-level apps in the USA.
Common React Component Security Vulnerabilities
React’s declarative nature helps prevent many traditional web security issues, but it’s not immune to vulnerabilities. Here are the main ones I’ve encountered:
1. Cross-Site Scripting (XSS)
Despite React’s automatic escaping of content, XSS can still sneak in through:
- Using dangerouslySetInnerHTML improperly
- Inserting unsanitized user input into components
- Third-party libraries that manipulate the DOM
2. Injection Attacks
Injection attacks happen when untrusted data is passed directly into queries or commands. In React, this often occurs when integrating with backend APIs or databases without proper validation.
3. Insecure Component Props
Passing sensitive data or functions as props without proper validation can expose your app to logic flaws or data leaks.
4. Exposure of Sensitive Information
Accidentally rendering API keys, tokens, or user data in the component tree or console logs is a common mistake.
How to Secure React Components: Practical Methods
I’ve found that combining several methods helps build secure React apps. Here’s how I approach this:
Method 1: Avoid dangerouslySetInnerHTML or Sanitize Inputs
Using dangerouslySetInnerHTML is often necessary for rendering HTML content, but it opens the door for XSS if you’re not careful.
Best Practice: Always sanitize HTML content before injecting it.
Here’s a simple example using the dompurify library:
import React from 'react';
import DOMPurify from 'dompurify';
function SafeHtmlRenderer({ htmlContent }) {
const cleanHtml = DOMPurify.sanitize(htmlContent);
return <div dangerouslySetInnerHTML={{ __html: cleanHtml }} />;
}
// Usage example with user-generated content
const userInput = `<img src=x onerror=alert('XSS Attack') /> <p>Hello, USA users!</p>`;
export default function App() {
return (
<div>
<h1>Secure HTML Rendering</h1>
<SafeHtmlRenderer htmlContent={userInput} />
</div>
);
}You can see the output in the screenshot below.
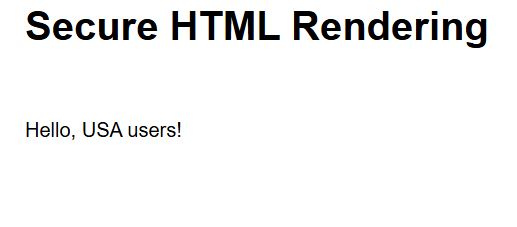
In this example, DOMPurify cleans the HTML string, removing any malicious scripts before rendering.
Method 2: Validate and Sanitize Props
Always validate props, especially if they come from external sources or user input.
Use PropTypes or TypeScript for type checking:
import PropTypes from 'prop-types';
function UserProfile({ username, age }) {
return (
<div>
<h2>Welcome, {username}</h2>
<p>Age: {age}</p>
</div>
);
}
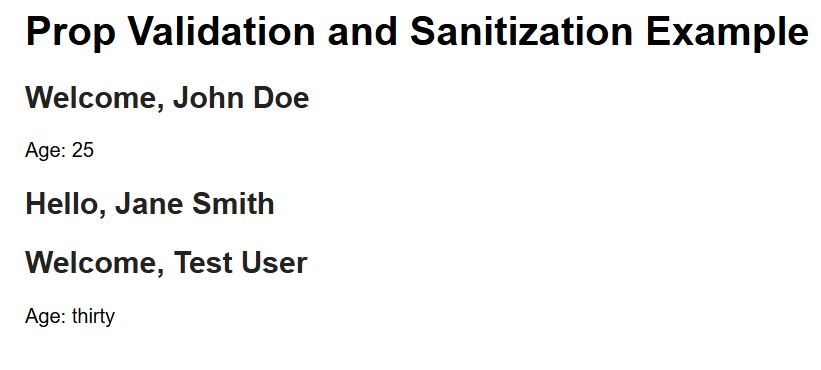
UserProfile.propTypes = {
username: PropTypes.string.isRequired,
age: PropTypes.number.isRequired,
};Additionally, sanitize strings to prevent injection:
import DOMPurify from 'dompurify';
function SafeUserProfile({ username }) {
const safeUsername = DOMPurify.sanitize(username);
return <h2>Hello, {safeUsername}</h2>;
}You can see the output in the screenshot below.
Method 3: Avoid Inline Event Handlers with Untrusted Data
Passing untrusted data directly into event handlers can lead to logic injection or unintended behavior.
Example of risky code:
<button onClick={() => eval(userInput)}>Click me</button>Better approach: Avoid eval or similar functions entirely. Always process or validate data before use.
Method 4: Secure API Calls and Handle Sensitive Data Properly
Never embed API keys or secrets directly in your React components. Use environment variables and server-side proxies.
Example:
// .env file
REACT_APP_API_URL=https://api.example.com
// API call in React
fetch(`${process.env.REACT_APP_API_URL}/data`)
.then(response => response.json())
.then(data => console.log(data));Make sure sensitive tokens are stored securely on the backend, not exposed in frontend code.
Method 5: Use Security-Focused Libraries and Tools
- Use Helmet for setting secure HTTP headers in React apps served by Node.js.
- Use CSP (Content Security Policy) headers to restrict what scripts can run.
- Regularly audit dependencies for vulnerabilities using tools like npm audit.
Example: Secure React Component with User Input
Here’s a full example combining these best practices:
import React, { useState } from 'react';
import DOMPurify from 'dompurify';
import PropTypes from 'prop-types';
function Comment({ text }) {
const safeText = DOMPurify.sanitize(text);
return <p>{safeText}</p>;
}
Comment.propTypes = {
text: PropTypes.string.isRequired,
};
export default function SecureCommentsApp() {
const [comment, setComment] = useState('');
const handleSubmit = (e) => {
e.preventDefault();
alert('Comment submitted safely!');
};
return (
<div>
<h1>USA React Comments</h1>
<form onSubmit={handleSubmit}>
<textarea
value={comment}
onChange={(e) => setComment(e.target.value)}
placeholder="Write your comment here"
/>
<button type="submit">Submit</button>
</form>
<h3>Preview:</h3>
<Comment text={comment} />
</div>
);
}You can see the output in the screenshot below.

This app sanitizes user input before rendering, preventing XSS attacks while allowing users to submit comments safely.
Keeping React components secure is an ongoing process. By avoiding dangerous practices like unchecked HTML injection, validating props, and handling sensitive data properly, you can protect your apps and users effectively.
If you’re building React apps for US-based businesses or users, where data privacy and security are critical, these practices become even more important.
You may also read:
- How to Convert a React Component to HTML
- React Router Redirect Component
- Convert a React Component to PDF
- React Components vs Containers

Bijay Kumar is an experienced Python and AI professional who enjoys helping developers learn modern technologies through practical tutorials and examples. His expertise includes Python development, Machine Learning, Artificial Intelligence, automation, and data analysis using libraries like Pandas, NumPy, TensorFlow, Matplotlib, SciPy, and Scikit-Learn. At PythonGuides.com, he shares in-depth guides designed for both beginners and experienced developers. More about us.

